Adversaries Action Procedures
Think Like They Act
Manage Your Detections and Hunts at the same level
Detection Coverage is Unique to Your Organization
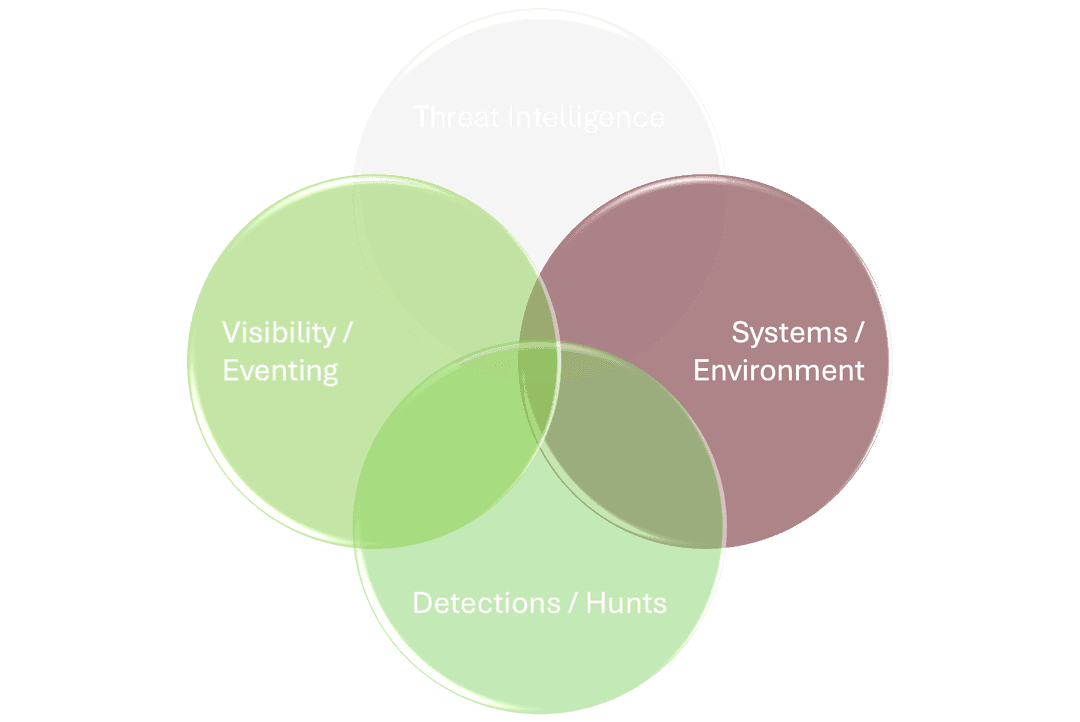
Threat Intelligence
Automatically ingest and organize your knowledge of the adversary at the procedural level. Cross reference between repositories of knowledge. Understand what the adversary can do. Identify gaps in what knowledge is actionable.
Visibility and Eventing
Automatically surface the correct log source and event across ALL of sysmon, ETW and common event sources. Integrate into your software pipelines to create and manage new eventing to provide visibility into shadow IT.
Detections and Hunts
Receive detailed detection coverage metrics at the procedural level. Understand how your coverage evolves as detections are added, threat intelligence shifts, and infrastructure grows. Identify the detections that will drive the greatest impact, with clear visibility into the artifacts and eventing needed to implement them.
Systems / Environment
Track detection coverage, opportunities and actions based upon the infrastructure deployed in your network. Integrate with your software development AI to create events and detections that align with your knowledge of threats, your current event formatting and work with your existing detections.
Use Cases
Track Actionable Metrics
Leadership doesn’t care how many alerts you triage or your false positive rates. They care how effectively you detect and respond to threats against their assets and infrastructure. Measure your organization’s ability to detect threats based on your knowledge of the adverary, and focus on the actions that will have the greatest impact on improving that coverage.
Manage Knowledge Across your SOC
Seamlessly integrate threat intelligence, red-team knowledge, detection engineering, and hunting to clearly understand your team's ability to identify threats. Focus on the actions that will have the greatest impact on improving coverage.
Detect Adversaries within Shadow IT
Custom software is a blind spot for many organizations. Identify the malicious techniques and procedures you care about. Proc-Docs works with your AI to identify which events should be added to custom software based on your priorities, ensure integration with your existing detections and supports creating new ones when necessary. Proc-Docs maintains your event dictionary, automatically suggesting the correct event for new detections from standard and custom log sources.
Identify Gaps in Coverage Across Cloud Platforms and Operating Systems
Your network is not monolithic. Continuously track how your detection coverage differs between cloud platforms or operating systems. Immediately action gaps in coverage, creating new detections or dispositioning gaps which are not applicable between platforms.
Request a Demo
Leave your information below and we will be in touch as we get closer to product release or to be considered for early access.